1. Article purpose[edit source]
The purpose of this article is to:
- briefly introduce the TAMP peripheral and its main features
- indicate the level of security supported by this hardware block
- explain how it can be allocated to the runtime contexts and linked to the corresponding software components
- explain, when necessary, how to configure the TAMP peripheral.
2. Peripheral overview[edit source]
The TAMP peripheral is used to prevent any attempt by an attacker to perform an unauthorized physical or electronic action against the device. It also includes the backup registers that remain powered-on when the platform is switched off.
2.1. Features[edit source]
Refer to the STM32MP13 reference manuals for the complete list of features, and to the software components, introduced below, to see which features are implemented.
2.2. Security support[edit source]
The TAMP is a secure peripheral. The access to some backup registers can be opened to the non-secure world via a direct configuration in TAMP, in secure mode.
3. Peripheral usage and associated software[edit source]
3.1. Boot time[edit source]
The TAMP is used at boot time to share data between the ROM code, FSBL and SSBL: see backup registers for further information. TAMP is also configured at boot time in OP-TEE to manage tamper events.
3.2. Runtime[edit source]
3.2.1. Overview[edit source]
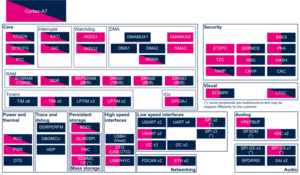
TAMP is seen as a system peripheral, the backup registers can be used by the Arm® Cortex®-A7 secure context with OP-TEE or the Arm® Cortex®-A7 non-secure context with Linux. The tamper detection and management is, after configuration, non modifiable.
3.2.2. Software frameworks[edit source]
| Domain | Peripheral | Software components | Comment | |
|---|---|---|---|---|
| OP-TEE | Linux | |||
| Security | TAMP | OP-TEE | Linux syscon framework[1] | |
For the Linux kernel configuration, sysconf part, please refer to TAMP device tree configuration.
For the secure configuration, please refer to TAMP device tree configuration and Tamper configuration.
3.2.3. Peripheral configuration[edit source]
The configuration is applied by the firmware running in the context to which the peripheral is assigned. The configuration can be done alone via the STM32CubeMX tool for all internal peripherals, and then manually completed (particularly for external peripherals), according to the information given in the corresponding software framework article.
3.2.4. Peripheral assignment[edit source]
Click on the right to expand the legend...
Check boxes illustrate the possible peripheral allocations supported by STM32 MPU Embedded Software:
- ☐ means that the peripheral can be assigned (☑) to the given runtime context.
- ⬚ means that the peripheral can be assigned to the given runtime context, but this configuration is not supported in STM32 MPU Embedded Software distribution.
- ✓ is used for system peripherals that cannot be unchecked because they are statically connected in the device.
Refer to How to assign an internal peripheral to a runtime context for more information on how to assign peripherals manually or via STM32CubeMX.
The present chapter describes STMicroelectronics recommendations or choice of implementation. Additional possiblities might be described in STM32MP13 reference manuals.
| Domain | Peripheral | Runtime allocation | Comment | ||
|---|---|---|---|---|---|
| Instance | Cortex-A7 secure (OP-TEE) |
Cortex-A7 non-secure (Linux) | |||
| Security | TAMP | TAMP | ✓ | ✓ | |
4. How to go further[edit source]
5. References[edit source]