Registered User mNo edit summary |
Registered User m (→Overview) |
||
| (13 intermediate revisions by 3 users not shown) | |||
| Line 1: | Line 1: | ||
<noinclude>{{ApplicableFor | |||
|MPUs list=STM32MP13x, STM32MP15x | |||
|MPUs checklist=STM32MP13x,STM32MP15x | |||
}}</noinclude> | |||
==Article purpose== | ==Article purpose== | ||
The purpose of this article is to briefly introduce the SYSRAM internal memory and indicate the level of security supported by this memory. | The purpose of this article is to briefly introduce the SYSRAM internal memory and indicate the level of security supported by this memory. | ||
==Peripheral overview== | ==Peripheral overview== | ||
The | The '''SYSRAM''' is an internal memory peripheral. It is physically located near the Arm<sup>®</sup> Cortex-A to optimize the core performance. | ||
* {{MicroprocessorDevice | device=13}} SYSRAM is 128-Kbyte wide | |||
* {{MicroprocessorDevice | device=15}} SYSRAM is 256-Kbyte wide | |||
===Features=== | ===Features=== | ||
Refer to the [[STM32MP15 resources#Reference manuals|STM32MP15 reference manuals]] for the complete list of features, and to the software components, introduced below, to see which features are really implemented. | Refer to the [[STM32MP13 resources#Reference manuals|STM32MP13 reference manuals]] or [[STM32MP15 resources#Reference manuals|STM32MP15 reference manuals]] for the complete list of features, and to the software components, introduced below, to see which features are really implemented. | ||
===Security support=== | ===Security support=== | ||
| Line 13: | Line 19: | ||
==Peripheral usage and associated software== | ==Peripheral usage and associated software== | ||
===Boot time=== | ===Boot time=== | ||
The [[ | ===== On {{MicroprocessorDevice | device=13}} ===== | ||
The [[STM32 MPU ROM code overview|ROM code]] leaves the SYSRAM secure when it jumps to the entry point of the FSBL that it just loaded into the SYSRAM.<br> | |||
The FSBL does not have to keep any context in SYSRAM when it jumps to the SSBL: each boot stage is independent from the other. | |||
===== On {{MicroprocessorDevice | device=15}} ===== | |||
The [[STM32 MPU ROM code overview|ROM code]] mainly configures the SYSRAM as a secure peripheral during its execution. It uses 9 Kbytes located at the beginning of the SYSRAM to store its read and write data. Among them, it stores the boot context in the first 512 bytes of SYSRAM: this boot context contains several information (such as the selected boot device) and pointers to the ROM code exported services (used for secure boot authentication). The ROM code loads the [[Boot chain overview|FSBL]] just after the boot context, into the remaining 247 Kbytes of SYSRAM, and eventually branches the Cortex<sup>®</sup>-A7 core 0 execution to this [[Boot chain overview|FSBL]].<br> | |||
The [[Boot chain overview|FSBL]] code can use the whole SYSRAM, but it must take care not to overwrite the boot context before taking it into account. | The [[Boot chain overview|FSBL]] code can use the whole SYSRAM, but it must take care not to overwrite the boot context before taking it into account. | ||
===Runtime=== | ===Runtime=== | ||
====Overview==== | ====Overview==== | ||
In STMicroelectronics distribution, the SYSRAM runtime mapping is the one reached at the end of the boot | In STMicroelectronics distribution, the SYSRAM runtime mapping is the one reached at the end of the boot, so it is fully secure. | ||
You may decide to split the SYSRAM at runtime. In this case: | You may decide to split the SYSRAM at runtime. In this case: | ||
* set the SYSRAM bottom secure, for | * set the SYSRAM bottom secure, for Cortex<sup>®</sup>-A7 secure services, from [[OP-TEE overview|OP-TEE]] | ||
and | and | ||
* set the SYSRAM top non-secure, for instance for using in Linux<sup>®</sup> as [[Reserved memory|reserved memory]] | * set the SYSRAM top non-secure, for instance for using in Linux<sup>®</sup> as [[Reserved memory|reserved memory]] | ||
{{Info | STM32MP13 embeds an on-the-fly DDR cyphering engine, the [[DDRMCE internal peripheral]], allowing to put secure sensitive code inside the external [[DDRCTRL and DDRPHYC internal peripherals |DDR]], instead of the SYSRAM}} | |||
====Software frameworks==== | ====Software frameworks==== | ||
{{: | ===== On {{MicroprocessorDevice | device=13}} ===== | ||
{{:STM32MP13 internal_peripherals_software_table_template}} | |||
| Core/RAM | | Core/RAM | ||
| [[SYSRAM internal memory|SYSRAM]] | | [[SYSRAM internal memory|SYSRAM]] | ||
| [[TF-A overview#BL32|TF-A overview]] | | [[OP-TEE overview|OP-TEE]] | ||
| [[Reserved memory|Linux reserved memory]] | |||
| | |||
|- | |||
|} | |||
===== On {{MicroprocessorDevice | device=15}} ===== | |||
{{:STM32MP15_internal_peripherals_software_table_template}} | |||
| Core/RAM | |||
| [[SYSRAM internal memory|SYSRAM]] | |||
| [[TF-A overview#BL32|TF-A BL32]] or [[OP-TEE overview|OP-TEE]] | |||
| [[Reserved memory|Linux reserved memory]] | | [[Reserved memory|Linux reserved memory]] | ||
| | | | ||
| Line 43: | Line 61: | ||
====Peripheral assignment==== | ====Peripheral assignment==== | ||
{{: | ===== On {{MicroprocessorDevice | device=13}} ===== | ||
< | {{:STM32MP13_internal_peripherals_assignment_table_template}} | ||
<section begin=stm32mp13 /> | |||
| rowspan="1" | Core/RAM | |||
| rowspan="1" | [[SYSRAM internal memory|SYSRAM]] | |||
| SYSRAM | |||
| <span title="assignable peripheral" style="font-size:21px">☐</span> | |||
| <span title="assignable peripheral" style="font-size:21px">☐</span> | |||
| Shareable (multiple choices supported) | |||
|- | |||
<section end=stm32mp13 /> | |||
|} | |||
===== On {{MicroprocessorDevice | device=15}} ===== | |||
{{:STM32MP15_internal_peripherals_assignment_table_template}} | |||
<section begin=stm32mp15 /> | |||
| rowspan="1" | Core/RAM | | rowspan="1" | Core/RAM | ||
| rowspan="1" | [[SYSRAM internal memory|SYSRAM]] | | rowspan="1" | [[SYSRAM internal memory|SYSRAM]] | ||
| Line 53: | Line 84: | ||
| Shareable (multiple choices supported) | | Shareable (multiple choices supported) | ||
|- | |- | ||
</ | <section end=stm32mp15 /> | ||
|} | |} | ||
Latest revision as of 15:08, 3 April 2023
1. Article purpose
The purpose of this article is to briefly introduce the SYSRAM internal memory and indicate the level of security supported by this memory.
2. Peripheral overview
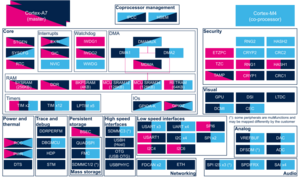
The SYSRAM is an internal memory peripheral. It is physically located near the Arm® Cortex-A to optimize the core performance.
2.1. Features
Refer to the STM32MP13 reference manuals or STM32MP15 reference manuals for the complete list of features, and to the software components, introduced below, to see which features are really implemented.
2.2. Security support
The SYSRAM is a secure peripheral (under ETZPC TrustZone memory adapter (TZMA)): it can be split into a secure and a non-secure regions with a 4-Kbyte granularity.
3. Peripheral usage and associated software
3.1. Boot time
3.1.1. On STM32MP13x lines 
The ROM code leaves the SYSRAM secure when it jumps to the entry point of the FSBL that it just loaded into the SYSRAM.
The FSBL does not have to keep any context in SYSRAM when it jumps to the SSBL: each boot stage is independent from the other.
3.1.2. On STM32MP15x lines 
The ROM code mainly configures the SYSRAM as a secure peripheral during its execution. It uses 9 Kbytes located at the beginning of the SYSRAM to store its read and write data. Among them, it stores the boot context in the first 512 bytes of SYSRAM: this boot context contains several information (such as the selected boot device) and pointers to the ROM code exported services (used for secure boot authentication). The ROM code loads the FSBL just after the boot context, into the remaining 247 Kbytes of SYSRAM, and eventually branches the Cortex®-A7 core 0 execution to this FSBL.
The FSBL code can use the whole SYSRAM, but it must take care not to overwrite the boot context before taking it into account.
3.2. Runtime
3.2.1. Overview
In STMicroelectronics distribution, the SYSRAM runtime mapping is the one reached at the end of the boot, so it is fully secure.
You may decide to split the SYSRAM at runtime. In this case:
- set the SYSRAM bottom secure, for Cortex®-A7 secure services, from OP-TEE
and
- set the SYSRAM top non-secure, for instance for using in Linux® as reserved memory
3.2.2. Software frameworks
3.2.2.1. On STM32MP13x lines 
| Domain | Peripheral | Software components | Comment | |
|---|---|---|---|---|
| OP-TEE | Linux | |||
| Core/RAM | SYSRAM | OP-TEE | Linux reserved memory | |
3.2.2.2. On STM32MP15x lines 
| Domain | Peripheral | Software components | Comment | ||
|---|---|---|---|---|---|
| OP-TEE | Linux | STM32Cube | |||
| Core/RAM | SYSRAM | TF-A BL32 or OP-TEE | Linux reserved memory | ||
3.2.3. Peripheral configuration
The configuration is applied by the firmware running in the context to which the peripheral is assigned. The configuration can be done alone via the STM32CubeMX tool for all internal peripherals, and then manually completed (particularly for external peripherals), according to the information given in the corresponding software framework article.
3.2.4. Peripheral assignment
3.2.4.1. On STM32MP13x lines 
Click on the right to expand the legend...
| Domain | Peripheral | Runtime allocation | Comment | ||
|---|---|---|---|---|---|
| Instance | Cortex-A7 secure (OP-TEE) |
Cortex-A7 non-secure (Linux) | |||
| Core/RAM | SYSRAM | SYSRAM | ☐ | ☐ | Shareable (multiple choices supported) |
3.2.4.2. On STM32MP15x lines 
Click on the right to expand the legend...
| Domain | Peripheral | Runtime allocation | Comment | |||
|---|---|---|---|---|---|---|
| Instance | Cortex-A7 secure (OP-TEE) |
Cortex-A7 non-secure (Linux) |
Cortex-M4 (STM32Cube) | |||
| Core/RAM | SYSRAM | SYSRAM | ☐ | ☐ | Shareable (multiple choices supported) | |
4. References